MAY 25, 8 am – 2 pm
600 West Shore Blvd, Pickering
<– Click for details
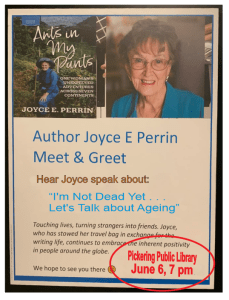
Joyce E. Perrin, a model for a Seniors.
Rather than be ANTI-AGING,
she’s a model for PRO-LIVING!
She is giving a talk on…
“I’m not dead yet…let’s talk about Ageing”
Pickering Public Library
June 6, 7 pm



 POINT-COUNTERPOINT: Govts paying lip service to problems of FOOD BANK use - Food bank lines prove we've lost our way Toronto Star, May 12, 2024 NICK SAUL AND VALERIE TARASUK CONTRIBUTORS The long lineups of bundle buggies, anxiety and despair in front… … Continue reading
POINT-COUNTERPOINT: Govts paying lip service to problems of FOOD BANK use - Food bank lines prove we've lost our way Toronto Star, May 12, 2024 NICK SAUL AND VALERIE TARASUK CONTRIBUTORS The long lineups of bundle buggies, anxiety and despair in front… … Continue reading  HEALTH: Be aware of TICKS risks for you and your pet - Ticks are bloodsucking creatures found throughout Canada. They are active in the spring through to the fall. Common species include the black-legged tick, also known as the deer tick, the… … Continue reading
HEALTH: Be aware of TICKS risks for you and your pet - Ticks are bloodsucking creatures found throughout Canada. They are active in the spring through to the fall. Common species include the black-legged tick, also known as the deer tick, the… … Continue reading  POINT-COUNTERPOINT: Pickering cashes in housing chips but at what ante? - The City of Pickering received more than $5 million from the Provincial Government for achieving and surpassing the home building objectives. Bully for it....are the home prices going to be… … Continue reading
POINT-COUNTERPOINT: Pickering cashes in housing chips but at what ante? - The City of Pickering received more than $5 million from the Provincial Government for achieving and surpassing the home building objectives. Bully for it....are the home prices going to be… … Continue reading  HEALTH: Move your butt to retain your memory! - It Ain't Over Yet By Michael McFarland My hearts in the right place; what's left of it, I guess My heart ain't the problem; it's my mind that's a total… … Continue reading
HEALTH: Move your butt to retain your memory! - It Ain't Over Yet By Michael McFarland My hearts in the right place; what's left of it, I guess My heart ain't the problem; it's my mind that's a total… … Continue reading  SHUT UP, YOU’RE PRETTY, Tea Mutonji - SHUT UP, YOU'RE PRETTY By Tea Mutonji Synopsis In Téa Mutonji's disarming debut story collection, a woman contemplates her Congolese traditions during a family wedding, a teenage girl looks for… … Continue reading
SHUT UP, YOU’RE PRETTY, Tea Mutonji - SHUT UP, YOU'RE PRETTY By Tea Mutonji Synopsis In Téa Mutonji's disarming debut story collection, a woman contemplates her Congolese traditions during a family wedding, a teenage girl looks for… … Continue reading ![]() EDITORIAL: ‘O CANADA’ – A response to Thomas Caldwell, Caldwells Securities - <-- [This FULL PAGE AD appeared in the Toronto Star, Sunday, May 5,2024] A couple of points to consider, Mr. Caldwell... When You write a glowing, heart-warming bit of nostalgia… … Continue reading
EDITORIAL: ‘O CANADA’ – A response to Thomas Caldwell, Caldwells Securities - <-- [This FULL PAGE AD appeared in the Toronto Star, Sunday, May 5,2024] A couple of points to consider, Mr. Caldwell... When You write a glowing, heart-warming bit of nostalgia… … Continue reading  FIGHT MOSQUITOES: Remove stagnant water from you yard - Mosquitoes are more than just a seasonal nuisance - they pose serious health risks. As warmer weather approaches, mosquitoes will become more active and abundant. These pests can transmit dangerous… … Continue reading
FIGHT MOSQUITOES: Remove stagnant water from you yard - Mosquitoes are more than just a seasonal nuisance - they pose serious health risks. As warmer weather approaches, mosquitoes will become more active and abundant. These pests can transmit dangerous… … Continue reading  PICKERING COUNCIL: BRENNER MAY Newsletter - Councillor Brenner, Region & Ward 1 Councillor, has a very comprehensive newsletter that covers a broad range of topics including...hold your breath now: Fire Safety Rabies Clinic for Pickering pets… … Continue reading
PICKERING COUNCIL: BRENNER MAY Newsletter - Councillor Brenner, Region & Ward 1 Councillor, has a very comprehensive newsletter that covers a broad range of topics including...hold your breath now: Fire Safety Rabies Clinic for Pickering pets… … Continue reading  EDITORIAL: Food Banks … we’re perpetuating them, NOT ELIMINATING THEM - FOOD BANK use - sky rocketing...up 80% since the pandemic. FOOD BANK donations - declining like a stone...less than 30% of prepandemic levels. GLOBAL NEWS: --> FOOD BANKS CBS NEWS:… … Continue reading
EDITORIAL: Food Banks … we’re perpetuating them, NOT ELIMINATING THEM - FOOD BANK use - sky rocketing...up 80% since the pandemic. FOOD BANK donations - declining like a stone...less than 30% of prepandemic levels. GLOBAL NEWS: --> FOOD BANKS CBS NEWS:… … Continue reading  POLITICS: TorStar columnist Vinay Menon writes a great piece about insult trading between Junior and Petey in Ottawa - … Continue reading
POLITICS: TorStar columnist Vinay Menon writes a great piece about insult trading between Junior and Petey in Ottawa - … Continue reading  VITAL BINDER: Crucial home & personal data all in one place - Consider creating a VITAL BINDER which is a compilation of all your vital information in one place. Make two copies: digital copy for storage on your computer and a hard… … Continue reading
VITAL BINDER: Crucial home & personal data all in one place - Consider creating a VITAL BINDER which is a compilation of all your vital information in one place. Make two copies: digital copy for storage on your computer and a hard… … Continue reading